Introduction
An http cookie is a small piece of data websites use to remember you. It lives in your browser. Servers send it. Browsers save it. Cookies help sites know you across pages. They let shopping carts keep items. They let sites remember a language. They also help measure site visits. This article explains what an http cookie is and how it works. I will use simple words and short sentences. You will see clear examples and good tips. The goal is trust and clarity. You will learn how to protect users and build better sites. Read on for practical steps and plain examples about the http cookie.
What is an http cookie?
A cookie is like a tiny note the web keeps for you. An http cookie is that note. A website sends it to your browser. Your browser stores it. Later, the browser sends it back to the site. This happens with each request to the site. Cookies can hold a name, a value, and rules. These rules control who can read the cookie. They can set when it expires. Cookies are not programs. They are small text strings. They do not run code by themselves. An http cookie helps the web remember choices. It makes the web feel smoother and friendlier. Think of it like a sticky label on a page that the site reads later.
A short history of the http cookie
The web did not start with cookies. Early web pages were simple. They forgot who you were between pages. Developers wanted a way to keep state. So cookies arrived. The first cookie idea became a standard. Over time, browsers added features. Sites used cookies for logins and carts. Then privacy concerns grew. Laws like GDPR changed rules for cookies. Browsers added new protections. The http cookie evolved with the web. It now has attributes for security and privacy. Those features help protect users while keeping useful functionality. The web community keeps improving cookie rules to match user needs and privacy laws.
How cookies work in browsers
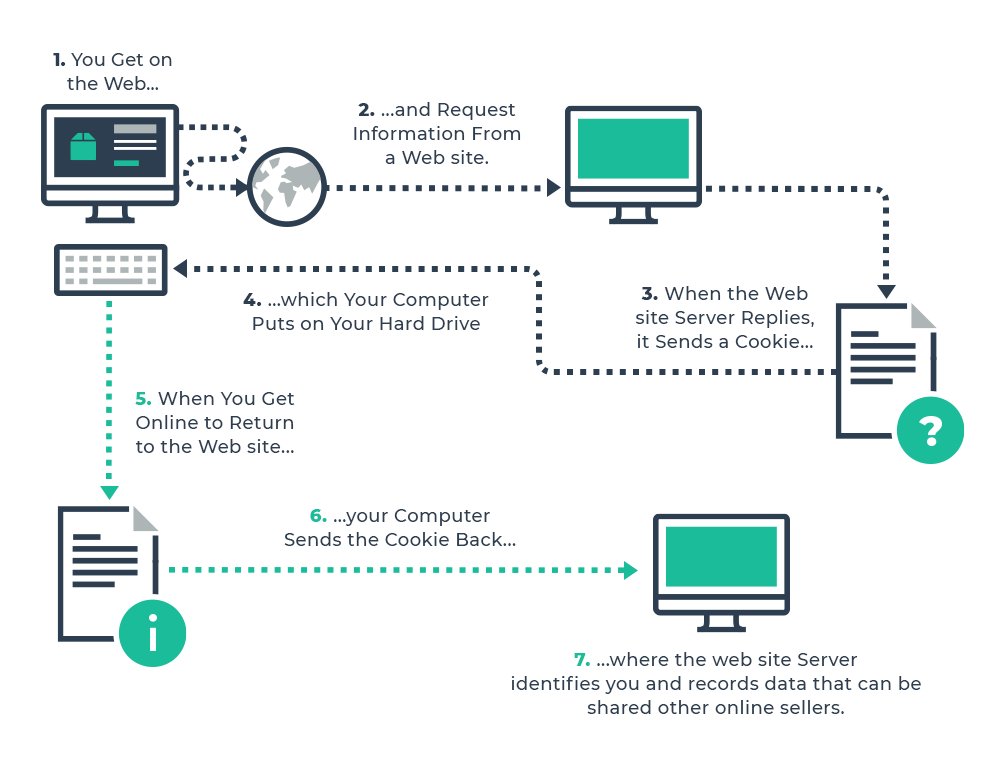
When a server replies to a browser, it can send a cookie. The header name is Set-Cookie. The browser stores that data. Later, the browser sends that cookie in the Cookie header. It sends the cookie for matching domain and path. Cookies can be limited to secure connections. They can be blocked from scripts. The browser follows these rules automatically. You usually do not see the details. But developers can read and set cookies with servers. A well-made site uses cookies only when needed. This helps reduce risk and improve speed. A clear workflow helps the http cookie do its job without hassle.
Cookie attributes you should know
Cookies come with helpful attributes. Domain and Path control scope. Expires and Max-Age set lifetime. Secure makes a cookie send only over HTTPS. HttpOnly blocks access from JavaScript. SameSite helps reduce cross-site risks. Together these shape cookie behavior. Use them to tighten security. For example, set HttpOnly on session cookies. Use Secure on all cookies sent over TLS. Use SameSite=Lax or Strict for sensitive tokens. These flags make the http cookie safer. They also prevent common attacks. Good defaults reduce surprises for users and developers.
Types of cookies and when to use them
There are many cookie types. Session cookies live while a browser tab is open. Persistent cookies last after the tab closes. First-party cookies come from the site you visit. Third-party cookies come from other sites or trackers. Secure cookies require HTTPS. HttpOnly cookies block script access. SameSite controls cross-site sending. Use session cookies for login sessions. Use persistent cookies for language or theme preferences. Avoid unnecessary third-party cookies to protect privacy. Choose the cookie type that fits the need. Thoughtful use of an http cookie keeps sites friendly and compliant.
Common use cases for cookies
Cookies enable many helpful tasks. Shopping carts use cookies to remember items. Login systems use cookies to keep you signed in. Preference settings use cookies for themes or language. Analytics tools use cookies to count visits. Feature flags can use cookies to test new ideas. Cookies can smooth slow workflows. For example, a site can store a draft with a cookie or local save. When used well, an http cookie improves user flow. It can make sites feel personal without heavy setup. Always ask if a cookie is truly needed for the feature before adding it.
Security risks with cookies
Cookies can be risky without care. An attacker can steal cookies via cross-site scripting. That can let them impersonate a user. Cross-site request forgery can misuse cookies sent automatically. If cookies are sent over HTTP, a network eavesdropper could read them. Misconfigured Domain and Path can expose cookies to other sites. Persistent cookies can leak privacy information over time. To fight these issues, use HttpOnly and Secure. Use SameSite to limit cross-site sending. Rotate session tokens and use short lifetimes for sensitive cookies. These steps keep any http cookie safer from common attacks.
Best practices for developers
Start small with cookies. Store only what you must. Use short lifetimes for tokens. Mark cookies HttpOnly when scripts do not need them. Always set Secure in production. Use SameSite to limit cross-site use. Avoid storing sensitive data in plain text. Prefer a server-side session tied to a token in the cookie. Validate cookies on the server. Log and monitor unusual cookie patterns. Add clear cookie notices for users if required. Test cookie behavior in real browsers. These steps make an http cookie work well and stay secure.
Privacy and legal concerns
Many regions require consent for some cookies. GDPR and ePrivacy rules are strict in parts of the world. Some cookies need explicit user permission. Analytics cookies, advertising cookies, and tracking cookies often fall under rules. Always present a clear cookie policy and consent option if laws require it. Offer a way to opt out. Keep records of consent when necessary. Minimize third-party cookies to reduce risk. Respect user choices and privacy settings. That builds trust. Treat the http cookie with care when dealing with personal data.
How users can manage cookies
Browsers let users control cookies. You can block third-party cookies in settings. You can clear cookies for one site or all sites. Many browsers offer private or incognito modes. These modes limit or delete cookies at session end. Extensions can block trackers and cookies. On mobile, check app settings for web views. If a site asks for consent, read the options carefully. Use strong browser defaults to protect yourself. For people who value privacy, disabling unnecessary cookies helps. Teaching users simple steps helps them manage any http cookie that affects their data.
Cookies vs other web storage
Cookies are not the only storage option. localStorage and sessionStorage are browser APIs. They let scripts store larger data. IndexedDB stores structured data in the browser. Cookies are sent with HTTP requests. Storage APIs are not. That difference matters. Use cookies for small, server-read tokens. Use localStorage for client-only data like UI state. Avoid storing sensitive tokens in localStorage. Scripts can read localStorage, so XSS is a risk. The http cookie is still the best choice for server session tokens when you use HttpOnly and Secure.
Debugging cookies and tools
Modern browsers have great dev tools. Open the network tab to see Set-Cookie headers. Use the Application or Storage tab to view stored cookies. Check cookie attributes like Secure and HttpOnly. Use curl to test server responses. For example, run a request and inspect headers to confirm cookies. Logging on the server side helps diagnose cookie flow. There are browser extensions that show cookie chains. Testing on different browsers reveals subtle differences. Good debug steps prevent surprises. Knowing how an http cookie moves from server to browser solves many common bugs.
Common myths about cookies
Some myths sound true but are not. Myth: Cookies are programs that run on your device. False. Cookies are text. Myth: Cookies always spy on you. Not true. Many cookies keep basic settings. Myth: Deleting cookies breaks everything. Not usually. It may log you out from sites. Myth: Cookies can crash your computer. False. They are small and simple. Understanding facts helps everyone make good choices. Treat the http cookie as a helpful tool when used responsibly. Busting myths helps teams design better privacy-first features.
The future of cookies and tracking
Web standards change over time. Some browsers limit third-party cookies. New privacy signals appear to replace old tracking methods. Server-side analytics and privacy-preserving APIs are gaining attention. Concepts like privacy sandboxes are being explored. That will change how websites use cookies. But the need to remember user choices will stay. Developers should design flexible systems that do not rely only on third-party cookies. Use first-party data responsibly. Keep an eye on browser changes. Prepare to adapt cookie use as rules evolve. A modern approach treats the http cookie as one of many tools, not the only one.
Simple implementation example
Here is a basic example of a server setting a cookie via headers. The server sends a Set-Cookie header. It may include attributes like Path, Secure, HttpOnly, and SameSite. A typical header looks like this: Set-Cookie: sessionId=abc123; Path=/; HttpOnly; Secure; SameSite=Lax; Max-Age=3600. The browser stores it and sends it on matching requests. You can test this with curl -I or in your browser dev tools. Use a short life for session cookies. Store sensitive data server-side. This example shows how an http cookie is part of a safe pattern.
Real example: shopping cart flow
Imagine an online shop. You add an item to your cart. The server sets a cookie with a cart ID. The browser stores that cookie. When you move to another page, the browser sends the cookie with the cart ID. The server uses that ID to show your cart items. If you log in, the server can merge the cart into your account. This flow uses a small http cookie to track the cart. It avoids storing all data in the cookie. The server keeps the full cart. This keeps cookies light and fast. Simple patterns like this work well in many sites.
Monitoring and auditing cookie use
Track the cookies your site sets. Make an inventory. Note which cookies are essential and which are optional. Classify them as functional, analytics, or marketing. Review third-party scripts that may add cookies. Set up periodic audits. Remove cookies that no longer add value. Use server logs to spot odd cookie values. Periodic reviews help with compliance. They also help performance. A tidy cookie setup reduces risk for both the team and users. Treat cookie audits as part of site health checks rather than a one-time job.
FAQ 1 — What exactly is a cookie?
A cookie is a small piece of text. It stores a name and a value. A website can send it to your browser. The browser keeps it and sends it back later. Cookies can also include rules about who can read them. They help websites remember choices across pages. They do not run code on your device. A cookie is not a file in most browsers. It is stored in the browser database. Managing cookies helps users keep control of their data.
FAQ 2 — Are cookies safe?
Cookies can be safe with care. Use Secure to require HTTPS. Use HttpOnly to block script access. Use SameSite to limit cross-site use. Avoid putting secrets directly inside cookies. Rotate session tokens often. Limit cookie lifetime for sensitive data. Also keep server validation strong. Proper use of cookies reduces many risks. When developers follow best practices, cookies remain a safe tool for session and preference handling.
FAQ 3 — Can I block cookies and still use sites?
Yes, but some features may break. Basic browsing works without cookies. Features like login or shopping carts may not work. Some sites offer cookie-free ways to work. Many sites give you consent options. You can block third-party cookies and still use most sites well. Use private browsing to limit cookie lifetime. Choose settings that match your privacy comfort level.
FAQ 4 — What is SameSite and why it matters?
SameSite is a cookie attribute. It tells the browser when to send a cookie across sites. Strict blocks cross-site sending. Lax allows some safe cross-site cases. None allows cross-site sending but requires Secure. SameSite helps stop CSRF attacks. Use Lax or Strict for sensitive session cookies. For less sensitive cookies, choose None only if needed and mark Secure. It is a simple rule that improves cookie safety.
FAQ 5 — Should I store tokens in localStorage instead of cookies?
Not for sensitive tokens. localStorage is readable by scripts. XSS vulnerabilities can expose those tokens. Cookies can be HttpOnly, blocking scripts. If you must use localStorage, harden your app against XSS. Better is to store session tokens in HttpOnly cookies. Then validate on the server. This pattern reduces token theft risk and keeps client code simpler.
FAQ 6 — How many cookies can a site set?
Browsers impose limits. They usually limit the number of cookies per domain and the size per cookie. Common limits are a few hundred cookies per browser. Each cookie typically can be around 4 KB. Avoid hitting limits by using compact tokens. Clean up expired cookies. Store minimal data in cookies. When designing, assume there are limits. Keeping cookie size small helps performance and stability.
Conclusion and next steps
An http cookie is a small tool with big impact. It helps sites remember choices and manage sessions. Use the cookie attributes to improve security. Choose short lifetimes for sensitive tokens. Limit third-party cookies to protect privacy. Audit cookie use regularly. Teach users how to manage cookies in their browser. If you build sites, prefer server-side storage for sensitive data. Test cookie behavior in real browsers. If you need help implementing a safe cookie pattern, ask for a small example. Clear design and good defaults make the web friendlier and safer for everyone.